Usually it is easier to block websites on your network router (switch or Wi-Fi access point you are using to access the Internet) or using third-party software (content filters, DNS filters, etc.).
Blocking Websites Using the Hosts File in Windows
The most popular method to block a specific website on Windows is to edit the hosts file. Usually it is located in %windir%\system32\drivers\etc\ directory. Please note that hosts file does not have an extension.
The path to the directory containing hosts file is set in the DataBasePath parameter under the registry key HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters. By default it is %SystemRoot%\System32\drivers\etc.
The hosts file is used to manually assign mappings between IP addresses and DNS names. When resolving names, the hosts has higher priority than DNS servers specified in the network connection settings.
To block a specific website (for example, facebook.com), open the hosts file (with the administrator privileges) and add the strings like these to it:
127.0.0.1 facebook.com
127.0.0.1 www.facebook.com
Save the file and restart your computer (or clear the DNS cache using the command: ipconfig /flushdns).
After that, when trying to open the facebook.com in any browser you will see the message
Page not found / Page not available.
You can add new lines containing website URLs to your hosts file using such a .bat file:
@echo off
set hostspath=%windir%\System32\drivers\etc\hosts
echo 127.0.0.1 www.facebook.com >> %hostspath%
echo 127.0.0.1 facebook.com >> %hostspath%
exit
Or you can use the following PowerShell functions to automatically block specific websites in your hosts file.
Function BlockSiteHosts ( [Parameter(Mandatory=$true)]$Url) {
$hosts = 'C:\Windows\System32\drivers\etc\hosts'
$is_blocked = Get-Content -Path $hosts |
Select-String -Pattern ([regex]::Escape($Url))
If(-not $is_blocked) {
$hoststr="127.0.0.1 ” + $Url
Add-Content -Path $hosts -Value $hoststr
}
}
Function UnBlockSiteHosts ( [Parameter(Mandatory=$true)]$Url) {
$hosts = 'C:\Windows\System32\drivers\etc\hosts'
$is_blocked = Get-Content -Path $hosts |
Select-String -Pattern ([regex]::Escape($Url))
If($is_blocked) {
$newhosts = Get-Content -Path $hosts |
Where-Object {
$_ -notmatch ([regex]::Escape($Url))
}
Set-Content -Path $hosts -Value $newhosts
}
}
To add a website to the list of blocked URLs, just execute the command:
BlockSiteHosts ("twitter.com")
To unblock the website, run:
UnBlockSiteHosts ("twitter.com")
Block Website IP Address in Windows Defender Firewall
Also, you can block some websites using the built-in Windows Defender Firewall. The main disadvantage of this method is that you won’t be able to use the name of a domain or a website URL in the blocking rule. Windows Defender Firewall allows you to specify only an IP address or a subnet as a source/destination.
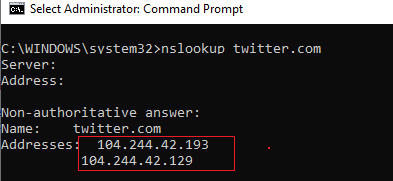
First of all, you have to get the IP address of the website you want to block. It is easier to do it using the nslookup command: nslookup twitter.com
1. After right click on the start icon and click Run and type:wf.msc and click OK. This will open the Windows Firewall with Advanced Security interface.
2. Click on Inbound Rules.
3. Click on New Rule. This opens the New Inbound Rule Wizard, which will guide you through adding your new firewall rule.
4. To begin creating an IP block rule, select the radio button next to Custom. Then press Next.
5. Now, make sure the radio button for All programs is selected and click Next.
6. The next screen asks you which ports and protocols your rule will apply to. Generally, with an IP block, you will leave this screen as it is, with the Protocol type set to Any. Click Next.
7. Now you can block the IP addresses. Look for the section with the header Which remote IP addresses does this rule apply to? Select the radio button next to These IP addresses.
8. Click Add. Type in the IP address you want to block and click OK. Repeat this for any IP addresses you want to block. You can also block IP address ranges. Once you've added all the IPs you want to block, click Next.
9. Select the radio button next to Block the connection and click Next.
10. For most IP blocks, you'll want to make sure all three boxes are checked: Domain, Private, and Public.
11. Name your rule. You can keep adding IP addresses to this rule, so make sure you name it something memorable! Then click Finish.
You've successfully added a rule in Windows Firewall to block any IPs you don't want accessing your server! If you ever need to add more IPs to this rule, double click on the rule to open the rule properties and click Scope. Then add new IP addresses just like you added them before.
Video:
You can also create a Firewall rule that blocks the connection to the website using PowerShell
Using this command, you can use a single IP address or range of IP addresses. Execute the following command in PowerShell:
The string “The rule was parsed successfully from the store” means that the new Firewall rule has been successfully applied. You can find it in the graphical interface of your Windows Defender Firewall.
Thus, you can convert the name of the website into its IP addresses and add a block rule to the firewall settings:
$IPAddress = Resolve-DnsName "twitter.com"| Select-Object -ExpandProperty IPAddress
New-NetFirewallRule -DisplayName "Block Site" -Direction Outbound –LocalPort Any -Protocol Any -Action Block -RemoteAddress $IPAddress
So you can now add a blocking rule to your Windows Firewall for multiple websites at once:
$SitesToBlock = "facebook.com","instagram.com","youtube.com"
$IPAddress = $SitesToBlock | Resolve-DnsName -NoHostsFile | Select-Object -ExpandProperty IPAddress
New-NetFirewallRule -DisplayName "Block Web Sites" -Direction Outbound –LocalPort Any -Protocol Any -Action Block -RemoteAddress $IPAddress
I have added the –NoHostsFile parameter to the Resolve-DnsName cmdlet in order not to use the hosts file for resolving.
Let’s make sure that a block outbound rule has appeared in the Windows Firewall console.



























No comments:
Post a Comment